A disciplined inventory of assets, connections, and dependencies frames the starting point for strengthening the digital network. It maps cloud, app, and network layers to reveal security gaps, data governance gaps, and threat surfaces. With posture assessed, a structured program—identity governance, zero-trust, and tiered segmentation—offers a path toward resilient operations. By aligning incident response, encryption, and observability, the approach promises measurable improvements, yet the next steps reveal more questions than answers.
How to Assess Your Current Digital Network Fortitude
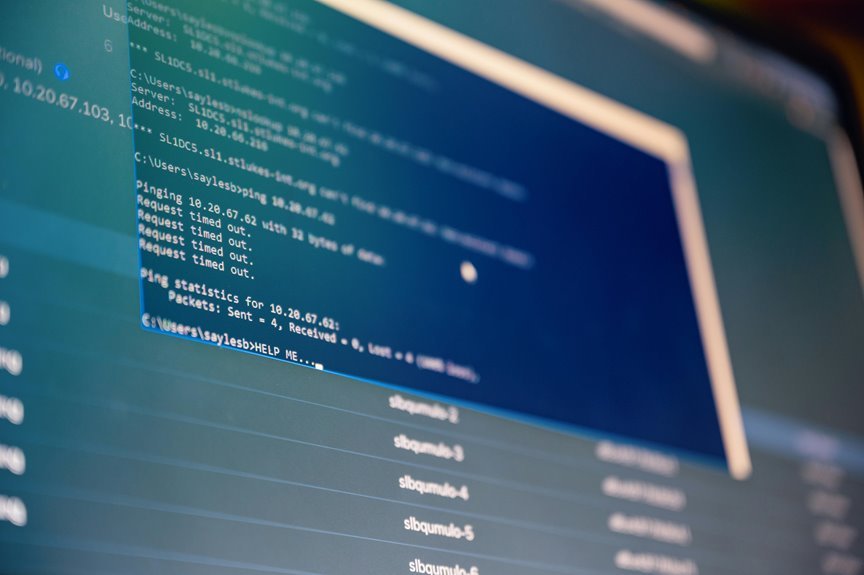
Assessing the current digital network fortitude begins with a structured inventory of assets, connections, and dependencies. The evaluation targets security posture, data governance, and threat modeling, then maps incident response capabilities. It weighs identity management and access controls against risk assessment, disaster recovery, and encryption standards. Security telemetry informs decisions, guiding precise improvements toward resilient, freedom-focused network stewardship.
Strengthening Security Across Cloud, App, and Network Layers
To fortify defenses across cloud, application, and network layers, the approach moves from inventory and risk scoring to implementing layered controls that align with evolving threat landscapes.
The piece analyzes security posture with threat modeling, focusing on cloud access, identity governance, and network segmentation.
It emphasizes incident response, data protection, zero trust, threat detection, disaster recovery, and ongoing improvement.
Optimizing Performance for Scale and Resilience
Optimizing performance for scale and resilience requires a disciplined approach that balances demand, reliability, and efficiency across heterogeneous environments. The analysis emphasizes measured capacity, load distribution, and continuity plans. It targets lowering scaling latency and accelerating recovery without overprovisioning. Resilience testing, observability, and deterministic failover policies enable confidence in peak load scenarios while preserving freedom to innovate.
Integrating Tools and Automations for Seamless Operations
Integrating tools and automations follows directly from the emphasis on scalable, resilient performance, aligning monitoring, deployment, and operational workflows into a unified, low-friction framework.
The approach emphasizes integrating tools and automations for seamless operations, enabling teams to orchestrate events, detect anomalies, and trigger responses with minimal friction.
Assessing fortitude, leaders quantify reliability, automate remediation, and preserve autonomy without sacrificing control or clarity.
Conclusion
In sum, the digital network stands as a pivoting fortress rather than a fixed bastion. With a clear-eyed inventory, layered zero-trust, and disciplined segmentation, resilience becomes a measurable discipline rather than a fleeting aim. Observability and automated remediation turn outages into predictable ripples, not deluges. As tools interlock and scale adapts, the system breathes with capacity and precision, delivering sustained performance and autonomy. The endgame: unwavering uptime through proactive, data-driven governance.